TL;DR: WordPress security requires layering multiple defenses: keeping core, themesA WordPress theme is a set of files that determine the design and layout of a website. It controls everything … More, and plugins updated on WordPress 6.7, using strong passwords with two-factor authentication, installing a reputable security pluginA plugin is a software component that adds specific features and functionality to your WordPress website. Esse… More, enforcing SSL, and choosing a host with server-level protection. Start with Step 1 (updates) today and work through all 10 steps to harden your site against the most common attack vectors.
Last Updated: April 2026
WordPress powers over 43% of all websites on the internet, making it the most popular CMS in the world and, inevitably, the most targeted. According to data tracked by the WordPress.org security team, the vast majority of compromised WordPress sites were running outdated software, weak credentials, or zero server-side protection at the time of the breach. The good news is that WordPress security is not complicated. It is a checklist. Work through these 10 steps and your site will be dramatically harder to compromise than the average installation.
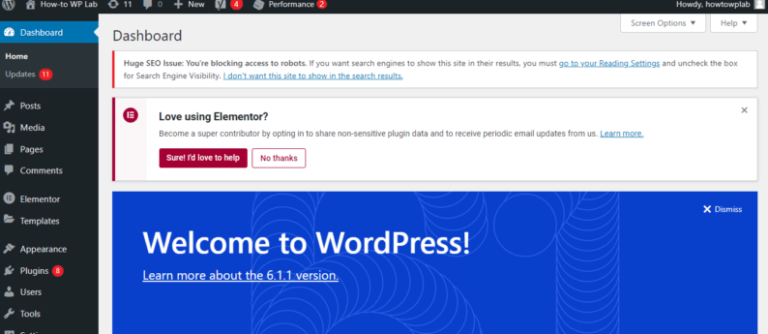
If you are brand new to WordPress and still getting oriented in the dashboardIn WordPress, the Dashboard is a central hub for managing a website’s content and settings. It is the first sc… More, read our beginner’s guide to logging in to WordPress first, then return here to lock things down.
Why WordPress Security Matters More Than Ever in 2026
Automated bots scan millions of URLs daily looking for outdated plugin versions, default admin usernames, and exposed login pagesIn WordPress, a page is a content type that is used to create non-dynamic pages on a website. Pages are typica… More. A site does not need to be large or profitable to attract an attack. Bots do not discriminate. They probe every IP addressAn IP Address (Internet Protocol Address) is a unique numerical identifier assigned to every device connected … More they can reach. When they find a vulnerability, they exploit it automatically, often injecting spam, malware, or a backdoor before the site owner notices anything is wrong.
The consequences of a compromised site range from embarrassing to devastating: Google blacklisting, lost customer data, hosting suspension, and hours of cleanup work. The 10 steps below address the most common attack vectors used against WordPress sites running PHP 8.3 and WordPress 6.7 in 2026.
Step 1: Keep WordPress Core, Themes, and Plugins Updated
Outdated software is responsible for the majority of successful WordPress attacks. Every update released by the WordPress core team or a plugin developer that mentions “security fix” is a public announcement of a vulnerability in the previous version. Attackers read those changelogs and immediately scan the web for sites still running the older, vulnerable version.
Enable automatic minor core updates in your wp-config.php by adding this line:
define( 'WP_AUTO_UPDATE_CORE', 'minor' );For plugins and themes, go to Dashboard, then Updates, and apply everything immediately. Review your installed plugins quarterly and remove any that have not been updated by the developer in over 12 months. Abandoned plugins are a liability, not a feature.
Step 2: Use Strong, Unique Passwords for Every Account
Brute force attacks guess common passwords at scale. If your WordPress admin password is short, reused from another service, or contains dictionary words, it can be cracked. Use WordPress’s built-in strong password generator when creating or updating user accounts. A strong password in 2026 is at least 16 characters, mixing uppercase, lowercase, numbers, and symbols.
Apply the same standard to your hosting account, databaseA database is an organized collection of data stored and accessed electronically. It is a crucial component of… More user, FTP credentials, and any email address tied to your domain. A single weak link in this chain is enough for an attacker to gain entry. Use a password manager such as Bitwarden or 1Password to generate and store credentials securely.
Step 3: Enable Two-Factor Authentication (2FA)
Two-factor authentication adds a second verification step beyond your password. Even if an attacker obtains your password, they cannot log in without the one-time code generated by your authentication app. This single step defeats the vast majority of credential-stuffing and brute force attacks against the WordPress login pageIn WordPress, a page is a content type that is used to create non-dynamic pages on a website. Pages are typica… More.
Plugins such as WP 2FA and Two Factor make adding 2FA straightforward. Both are actively maintained and available in the WordPress plugin repository. Configure 2FA for every administrator and editor account on your site, not just your own.
Step 4: Install a Reputable WordPress Security Plugin
A good WordPress security plugin provides malware scanning, login attempt limiting, firewall rules, and activity logging in a single package. These tools serve as an application-level firewall, blocking known malicious IP addresses and request patterns before they reach your site’s code.
The most widely used options in 2026 include Wordfence Security, Sucuri Security, and Solid Security (formerly iThemes Security). For a detailed comparison of the best options, see our guide to the 7 best WordPress security plugins. Each plugin has different strengths: Wordfence excels at real-time threat intelligence, Sucuri at external malware scanning, and Solid Security at login hardening and two-factor authentication integration.

Step 5: Force HTTPS with an SSL Certificate
Every WordPress site in 2026 should run exclusively over HTTPS. An SSL certificate encrypts data in transit between your visitor’s browser and your server, preventing man-in-the-middle attacks that could capture login credentials or session cookies. Google also uses HTTPS as a ranking signal and shows “Not Secure” warnings for HTTP sites in Chrome.
Most reputable hosts provide free SSL certificates via Let’s Encrypt. Once your SSL certificate is installed, enforce HTTPS site-wide by updating your WordPress address and site address in Settings, then General to use https://. Add this to your .htaccess file to redirect all HTTP traffic:
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]Step 6: Harden Your WordPress Login Page
The default WordPress login URL (wp-login.php) is known to every attacker. Bots hammer this URL with credential-stuffing attempts around the clock. Several hardening measures work well together:
- Limit login attempts: Block an IP after a set number of failed tries. Most security plugins include this feature.
- Change the login URL: Plugins such as WPS Hide Login let you move the login page to a custom path.
- Add a CAPTCHA: Google reCAPTCHA v3 or Cloudflare Turnstile stop automated bots without adding friction for real users.
- Rename the default admin username: If your administrator account is still named “admin,” create a new account with a unique username, assign it Administrator role, then delete the “admin” account.
Step 7: Set Correct WordPress File Permissions
Incorrect file permissions are a common vulnerability that allows attackers who gain access to one file to escalate to other parts of the server. WordPress has clear recommendations for file permission settings:
| Location | Recommended Permission | Notes |
|---|---|---|
| Directories | 755 | Owner can write; others can only read/execute |
| Files | 644 | Owner can write; others can only read |
| wp-config.php | 440 or 400 | Only owner (or owner + group) can read; no write |
| .htaccess | 644 | Writable only by owner |
You can set permissions via your hosting file manager or using SSH with the chmod command. Never set any file or directory to 777 (world-writable) on a production server.
Step 8: Disable the WordPress File Editor and XML-RPC
WordPress includes a built-in code editor under Appearance, then ThemeA WordPress theme is a set of files that determine the design and layout of a website. It controls everything … More File Editor and Plugins, then Plugin File Editor. If an attacker gains access to an administrator account, this editor lets them inject malicious code directly into your theme or plugin files. Disable it by adding this line to wp-config.php:
define( 'DISALLOW_FILE_EDIT', true );XML-RPC is a legacy remote publishing protocol that is frequently used to amplify brute force attacks. Unless you specifically need it for a mobile app or third-party integration, disable it entirely. Add this to your .htaccess or use a security plugin that provides this option with a single toggle:
<Files xmlrpc.php>
Order Deny,Allow
Deny from all
</Files>Step 9: Run Regular Backups to an Offsite Location
No WordPress security strategy is complete without a reliable backup system. If your site is ever compromised, a clean recent backup is the fastest path to recovery. Backups stored only on the same server as your site are useless if the server is compromised or the account is suspended.
Backup plugins such as UpdraftPlus, BackWPup, and Duplicator can automatically send copies of your database and files to remote storage such as Amazon S3, Google Drive, or Dropbox on a daily schedule. Keep at least 14 days of backup history so you can restore to a date before a breach that went unnoticed for several days.
Step 10: Choose Hosting with Built-In WordPress Security in 2026
All of the steps above operate at the application layer. Your hosting environment is the foundation that everything else rests on. A host with weak server security can undermine every plugin and configuration change you make. Conversely, a host with strong server-level protections acts as an additional layer of defense that operates independently of your WordPress installation.
When evaluating hosting for WordPress security, look for these specific features:
| Feature | What It Does | Best For |
|---|---|---|
| Imunify360 | Real-time malware scanning and intrusion detection at the server level | Sites that need proactive threat blocking without plugin overhead |
| Daily automated backups | Server-side backups independent of WordPress plugins | All sites; second layer of redundancy |
| PHP 8.3 support | Latest PHP version with improved performance and security patches | Sites running modern plugins compatible with PHP 8.x |
| Web Application Firewall (WAF) | Filters malicious requests before they reach WordPress | High-traffic or e-commerce sites |
| Free SSL provisioning | Automatic Let’s Encrypt SSL with auto-renewal | All sites |
| Isolated hosting accounts | Prevents cross-account contamination on shared servers | Shared hosting environments |
GigaPress managed WordPress hosting includes Imunify360 at the server level on all plans, running continuously to detect and neutralize threats without consuming your WordPress resources. Daily automated backups are included with every account, stored offsite and retained for 30 days. Hosting plans start at $2.40/month with a 99.9% uptime SLA. For a full breakdown of what is included, see our WordPress hosting packages.
For more context on what a complete hardening approach looks like at both the application and server level, see our companion guide: WordPress Security Hardening: 15 Steps to Protect Your Site in 2026.
WordPress Security Quick-Reference Summary
Here is a condensed checklist of all 10 steps for quick reference:
- Keep WordPress core (6.7+), all themes, and all plugins updated
- Use unique strong passwords (16+ characters) for every account
- Enable two-factor authentication for all admin accounts
- Install a security plugin (Wordfence, Sucuri, or Solid Security)
- Force HTTPS with a valid SSL certificate site-wide
- Harden the login page: limit attempts, rename admin user, add CAPTCHA
- Set correct file permissions (755 for directories, 644 for files, 440 for wp-config.php)
- Disable the file editor and XML-RPC via wp-config.php and .htaccess
- Schedule daily automated backups to an offsite location
- Host on a platform with Imunify360, WAF, and daily server-level backups
Ready to Upgrade Your Website?
If you’re looking for fast WordPress hosting and done-for-you updates, check out our hosting packages by clicking the button below. GigaPress includes Imunify360 malware protection, daily automated backups, and free SSL on every plan, giving you server-level WordPress security without any additional configuration.
Frequently Asked Questions About WordPress Security
Is WordPress secure out of the box?
WordPress core is developed with security in mind and receives regular security patches, but it is not fully hardened out of the box. The default installation exposes the login URL, includes the file editor, and has no login rate limiting. You need to apply the hardening steps in this guide to make it resistant to common attack vectors.
How do I know if my WordPress site has been hacked?
Common signs of a compromised WordPress site include: unexpected redirects to unfamiliar websites, Google Search showing warnings about your site, your hosting provider suspending your account for malware, unfamiliar admin users appearing in the Users list, and your security plugin flagging modified core files. Run a full malware scan with Wordfence or Sucuri immediately if you suspect a breach.
Do I need a security plugin if my host provides Imunify360?
Yes, and the two work together rather than replacing each other. Imunify360 operates at the server level, blocking threats before they reach WordPress. A security plugin like Wordfence operates at the application level, monitoring user logins, file changes, and WordPress-specific vulnerabilities. Both layers together provide substantially stronger protection than either alone.
How often should I back up my WordPress site?
At minimum, daily backups are recommended for any active site. If you publish frequently or run an e-commerce store with regular orders, consider twice-daily or real-time backups. Keep at least 14 to 30 days of backup history stored offsite so you can restore to a clean point before an undetected breach.
What is the most important WordPress security step?
Keeping software updated is the single most impactful security measure because the majority of successful attacks exploit known vulnerabilities in outdated plugins, themes, or WordPress core. Enable automatic minor core updates and review plugin updates weekly. All other hardening steps build on this foundation.